Aight! We’ve talked about Computer Science and we’ve talked about some design features used in blockchain. Now let’s put it all together and cap this series off.
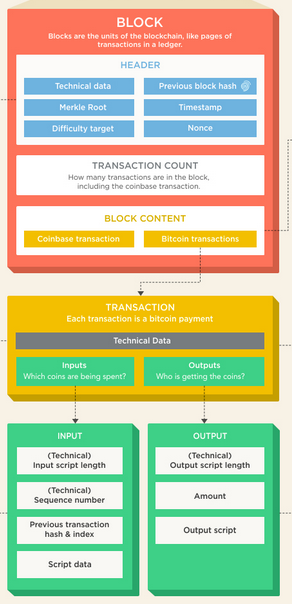
What is blockchain? It is a linked list of data structures that uses cryptographic hashing to sign each data structure, thus including it in the canonical chain. Here’s the block used by Bitcoin (most other cryptos will have mostly the same components).
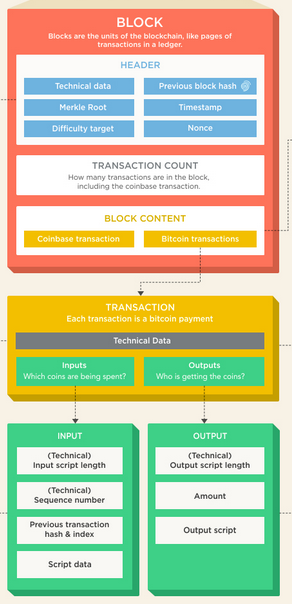
You can see the transactions in the Block Content section, and you can see info (such as the hash of the previous block) in the Header section. Let’s relate this all together and draw a true picture of a blockchain (specifically Bitcoin) block. To do so, we’re gonna be dealing with a whole bunch of cryptographic hashes.
Hashing: A Redux
If you want the nitty gritty detail, you can go here. However, since we’re not writing a mining algorithm or a storefront, I’ll spare you the minutae. If you want an awesome video that explains exactly what I’m about to talk about, but in visual form? Here ya go! Want to learn more about blockchain than you ever wanted to know, but all at a layperson level? You’re welcome!
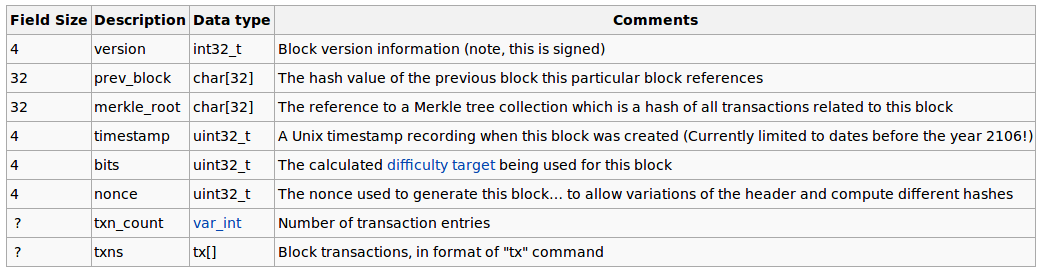
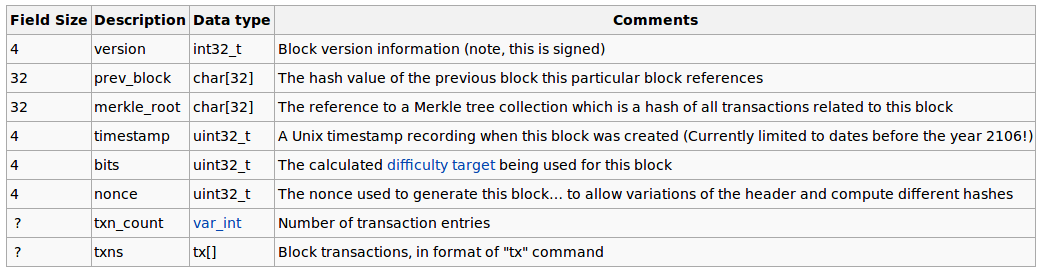
Here’s a Bitcoin block:
Let’s work from the bottom up.
txns
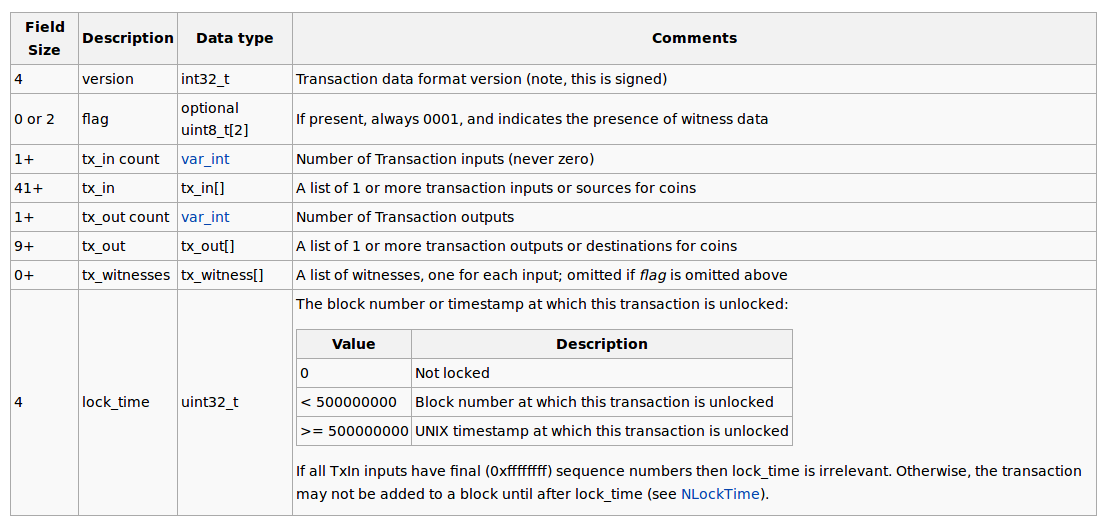
The payload of a Bitcoin block is an array of transactions. Each transaction looks like this:
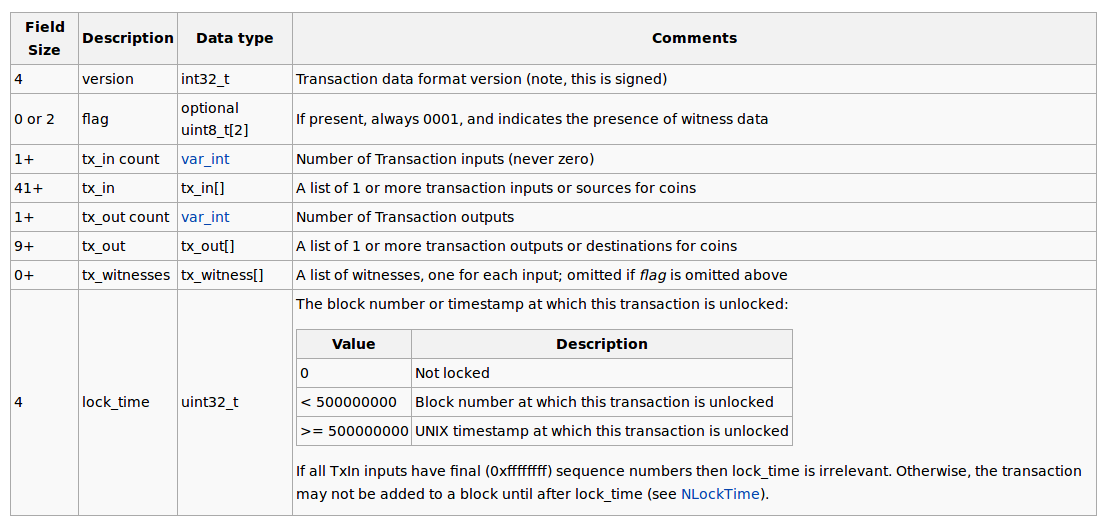
I show the transaction mainly to show you that it contains two things: tx_in and tx_out. This is how it works, you combine a certain number of prior transactions in the blockchain (inputs) and then dole out the coins contained in those transactions in the outputs. If the inputs go over how much you’re paying the other person, you add an output to pay yourself back the overage. It’s much like cash. Just like handing bills to the cashier and receiving change back, you hand over inputs, and receive back an output for the overage.
Let’s do a quick example. Oscar wants to pay ZARDOZ for the Gift of the Gun, and he wants to pay $150. Oscar has previously received money from Office Manager Mohammed for “Jihad related expenses” for the amount of $110. Oscar has also previously received money from Preet Bahahahaha for “Woodchipping services” in the amount of $65. In order to pay ZARDOZ, Oscar sets up the transaction by including the previous Jihad and Woodchipping transactions as inputs, and creates two outputs: one to ZARDOZ for $150, and one back to Oscar for the remainder ($25). Then those Jihad and Woodchipping transactions are marked as fulfilled, meaning that they can’t be used again as inputs.
txn_count
This is fairly self explanatory. This contains the number of transactions in the block.
nonce
From here on up in the block, everything is contained in the header. Remember that the hash of the block is really the hash of the header. The txn and txn_count parts of the block are not used in calculating the hash. However, we’ll find out really soon why the transactions are still reflected in the block hash.
Nonce is related to mining. I’ve alluded to the way that blocks are created, and I’ll discuss it more in the next section, but suffice it to say that the nonce is a random number and has no purpose besides in calculating the hash. The way that a block is added to the blockchain is that the block’s hash must be below a certain number. How do you get the hash below a certain number? You adjust the source data used to make the hash. Since the hash comes from the header and the nonce is in the header, you can change the nonce until the hash is below a certain number. Notice that simply changing the nonce to a lower number doesn’t guarantee that the hash is a lower number. This is where luck and random chance come into play. We’ll talk more in the next section about this.
bits
Bits goes with the nonce. It is the “certain number” mentioned above that the hash needs to go below for the block to be accepted.
timestamp
Timestamp is self explanatory. It’s the time when the block was created.
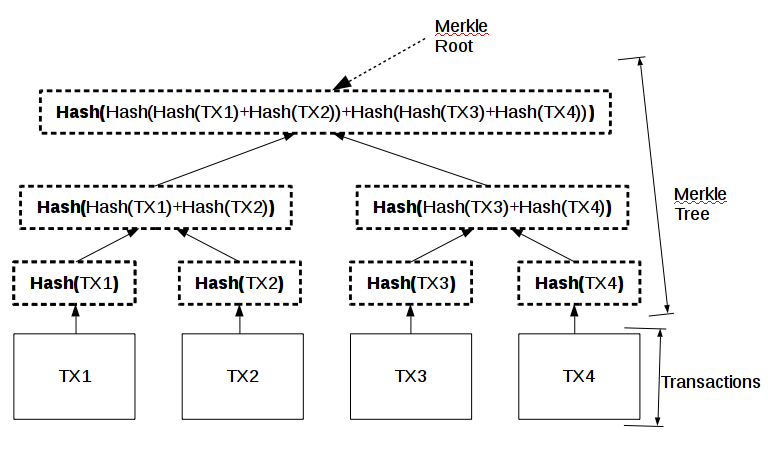
Merkle Root
We’ve discussed the Merkle root before, but haven’t really nailed it down. Let’s do that now. The 10,000 foot view is that the Merkle root is the hash of all of the transactions. The hash of the block (which is actually the hash of the block header) takes the Merkle root into account when calculated.
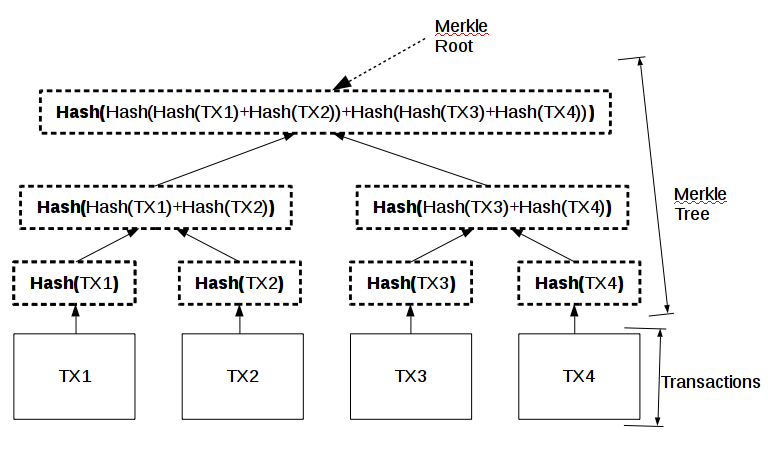
The Merkle tree is a binary tree (each parent node has two children) that hashes from the bottom up. The bottom row of the Merkle tree contains the hashes of each transaction. The middle row hashes adjacent bottom row hashes (it’s a hash of a hash). The top row is a hash of a hash of a hash and contains information from all of the transactions. Notice what it would take to modify or replace a transaction. If STEVE SMITH tries to replace TX4 with FAKE_TX4, he has to recalculate three different hashes, as well (all of the hashes that include TX4 in them).
Prev Hash
This has been discussed at length in the prior two parts. This is the hash of the prior block, the link between the current block and the prior block.
Version
The version of the blockchain tells everybody what rules this block has been assembled under. This makes it possible to improve a blockchain without having to toss out all of the old blocks.
Mining
We’ve hinted at what mining is already, but now we can put all the pieces together. When transactions are posted to the blockchain network (all of the computers mining and transacting on that blockchain), they are packaged up into a block to be added to the end of the blockchain. How this happens is technical and a bit beyond this overview. Once a block is packaged up, the mining process begins. The block, sans block hash and nonce, is sent out to the network for mining. Computers that are set up as miners begin to calculate the block hash. Remember that the block hash is calculated from data that includes the Merkle root, the previous block’s hash, and the nonce. All of those pieces of data are constant except for the nonce. Therefore, miners, upon calculating the block hash, adjust the nonce to try to get the block hash to be less than the current difficulty number (represented by the bits field).

Once a miner has calculated a block hash below the current difficulty number, they submit the hashed block to the network. If they’re the first to do so, they “win”. They end up getting a small payment of cryptocurrency for their efforts. The payment is based on an algorithm that reduces the amount of currency created for a successful mine until an end date when no more currency will be created for that coin. At that time, miners will only be compensated by transaction fees (which are currently in the tenths of a percent range).
As you can imagine, it’s not easy to do this. Bitcoin, for example, is designed so that, on average, the winner mines the block in about 10 minutes. Given the vast amount of processing power dedicated to Bitcoin mining across the world, the chance of a single desktop computer winning even once a month is slim. In some other cryptocurrencies, it is easier, but even a second tier crypto like Monero would average one or two wins a month for a standard desktop computer. At that point, you’re probably not making enough to pay for the electricity you used.
That’s where mining pools come in. It’s a fairly simple concept. Take a bunch of computers, let them mine as a cohesive unit, and split the winnings across members based on a pre-defined formula.
The Big Picture of Blockchain and Different Applications
We’ve talked about blockchain in the context of cryptos, but there are a ton of different potential applications for blockchain. The main “hot topic” for blockchain use is reputation analysis. Rather than having to go through a reputation broker (Uber, AirBnB, Yelp) to find out whether the person driving that car or renting that room or cooking that meal is trustworthy, you can reach out to the decentralized blockchain to find their reputation.
This is a fairly simplistic application of reputation analysis, but the reason folks are excited is the application of such a thing to automation technology. What if, for example, you didn’t have to put in a reservation to get a hotel room? If your reputation is high enough and the room is available, the lockbox automatically opens and gives you the key to the room. All you have to do is tell the system how long you plan on staying there, and you’re set.
Another application is identity management. Does the cashier really need to see your name, address, and other personal info to know that you’re old enough to buy alcohol? There’s a whole bunch of identity leakage that sets each and every one of us up for identity theft. One proposed use of blockchain is to provide customized identity services. The cashier can query the blockchain as to whether you’re old enough to buy alcohol, but can’t access your address. Amazon can get your address, but can’t get your social security number. Starbucks can get your first name, but not your last name.
What about securing your finances? This isn’t entirely separate from cryptocurrencies, but what if every transaction you made was from a different account? Instead of giving your bank account info or your credit card number to merchants, you give the equivalent of a Visa gift card with the exact amount of the transaction on it. If Target gets breached and your info is leaked to malevolent actors, it’s not an issue, because it points to an empty one-time account.
Finally, the application that I think would be the most interesting. Traffic management via blockchain. As automated cars become a more likely reality, most of the traffic management interaction methods that have been designed to be centralized or distributed in nature. A decentralized traffic management system would reduce the efficacy of government meddling and the potential for an enforced monopoly a la internet service provider.
Cryptocurrencies
I’m not going to list out all the cryptocurrencies in detail. I trust y’all to DDG it yourselves. Let me just point out a few of the big ones in passing.
Bitcoin – The original and most famous. There is relatively little anonymity in using Bitcoin, as shown by the Silk Road FBI takedown. It’s also relatively slow to get new blocks integrated, at an average of 10 minutes per block.
Bitcoin Cash – A fork of Bitcoin meant to scale to more users a bit easier by making the blocks bigger.
LiteCoin – Billed as “silver to Bitcoin’s gold”. It generates blocks 4x faster (2.5 minutes per block), will generate more coins than BitCoin, and some different internal algorithms.
Ethereum – Ethereum is much more than a cryptocurrency. It creates smart contracts that can take advantage of automation. Want to unlock your guestroom when somebody has enough reputation points? Ethereum is probably the best blockchain to start from to do this sort of thing.
Monero – Billed as the “secure cryptocurrency,” it is designed slightly differently from BitCoin so that bad actors (like the FBI) can’t trace one transaction back and see your entire transaction history. Secure is a relative term, because, as seen in the Silk Road incident, there are weaknesses wherever you have to give personal info (shipping, currency conversion)
Drawbacks and Limitations
This could be an article in and of itself, but I’ll just hit a few that are top of mind.
- Blockchain length – The immense size of the Bitcoin (and other large cryptos’) blockchain means that you either need to rely on somebody else’s node to get plugged in (by using an exchange) or you need to wait a few days for all of the blocks to be downloaded.
- Block acceptance time – In Bitcoin, it takes an average of 10 minutes for your transaction to be included in an accepted block, and due to forks (when two different blocks are accepted in two different parts of the network), folks recommend waiting an hour before declaring the transaction “completed.” That obviously doesn’t work for somebody trying to walk out the checkout line at the supermarket.
- Scalability – This is kinda wrapped up in the last two, but the number of transactions in a block are limited by a maximum size. Therefore, as more and more transactions occur, the chance of your transaction making the first block goes down substantially. Then, you have to wait not only 10 minutes for your block to be mined, but you have to wait an unknown amount of time until your transaction is included in a mined block. This is where transaction fees come into play. When there are 50,000 transactions, which ones are you going to try to make into a block as a miner? The ones that pay the best, of course.
- Security – We’ve discussed some security concerns already, but blockchain doesn’t resolve the single biggest threat in online transactions: the other party in the transaction retaining and ultimately misappropriating your personal information.
I hope this series was helpful to y’all! I’ve certainly learned a ton!